Procurement Fraud: How to Spot Signs and Prevent Schemes

Mekari Insight
- Procurement fraud can occur at every stage of the purchasing cycle, from planning and tendering to vendor selection and payment. It often hides within standard administrative procedures.
- Red flags such as bid rigging, contract splitting, duplicate invoices, and frequent contract amendments must be monitored proactively, not just during annual audits.
- An integrated procurement software Mekari Expense helps prevent fraud from the start through vendor verification, automated approvals, real-time audit trails, and centralized monitoring.
A manufacturing company discovered duplicate payments made to the same vendor over several months. Each transaction looked small and routine — but the total loss reached millions. After investigation, the root cause was clear: weak approval controls and poor vendor verification created the perfect opportunity for fraud.
Cases like this are more common than many organizations realize. Procurement fraud often hides behind “normal” processes and routine paperwork. To understand the risks and how to prevent them, let’s break it down step by step.
Procurement fraud
Procurement fraud is any intentional deception that happens during the purchasing process of goods or services. It can occur before, during, or after a contract is awarded.
In simple terms, it’s when someone manipulates the procurement process for personal gain — whether that’s money, influence, or unfair advantage.
Fraud can show up in many forms, such as:
- Inflated budgets or manipulated cost estimates
- Bid rigging during the Request for Proposal (RFP) stage
- Collusion between vendors
- Fake or duplicate invoices
- Billing for goods or services that were never delivered
Procurement fraud doesn’t only come from outside vendors. It can also involve internal employees who misuse their access, override controls, or collaborate with suppliers. In more sophisticated cases, fraudsters may exploit system vulnerabilities or conduct cyberattacks to manipulate procurement data.
Because procurement involves large budgets, multiple stakeholders, and complex documentation, it naturally creates risk exposure. Many organizations believe their controls are sufficient — until irregularities surface in audits or investigations.
How to identify procurement fraud
Detecting procurement fraud requires a structured approach. Below are practical steps organizations can use to identify warning signs early.
1. Procurement fraud indicator in Indonesia

In the Indonesian context, fraud risk can be flagged using structured indicators such as those developed under the Potential Fraud Analysis (PFA) method. These indicators help prioritize high-risk procurement activities.
Common red flags include:
- Unusual timeline gaps between tender announcement and winner selection
- Contract values that are extremely close to — or significantly different from — the estimated budget
- High-value contracts that receive limited scrutiny
- Very short tender titles or vague descriptions, which may signal low transparency
- Procurement clustered in the fourth quarter, often due to budget spending pressure
- Repeat winners, where the same company wins multiple contracts within a fiscal year
Each indicator alone may not prove fraud. However, patterns across multiple indicators significantly increase risk. Monitoring systems and data dashboards can help highlight these patterns in real time.
2. Review planning process
Fraud often begins long before the bidding stage. Reviewing the procurement planning phase is essential. Key things to examine:
- Was the project listed in the official procurement plan in advance?
- Are the volume, specifications, and scope clearly defined?
- Is the timeline realistic?
When a project appears suddenly without prior planning, it raises questions about urgency and justification. A lack of transparent planning may indicate attempts to bypass competition or fast-track certain vendors.
3. Identify similar procurements
Repeated procurement of similar projects in the same location can signal inefficiencies — or something more concerning.
For example, if a road is repaired every year using different materials, or a building undergoes repeated renovation within a short period, it may indicate poor quality execution, artificial project splitting, budget cycling, or deliberate manipulation to generate repeated contracts.
Looking at historical procurement data helps reveal patterns that a single project review might miss.
4. Review company track record
Understanding who is behind the winning vendor is crucial. Areas to verify:
- Company ownership and shareholder structure
- Possible affiliations with public officials
- Past contract history
- Whether the vendor has won contracts disproportionately
- Blacklist status or prior legal issues
A company with limited experience but frequent wins may require deeper review. Similarly, if only one bidder meets qualification requirements while others appear as “formal competitors,” it may indicate a staged competition.
Vendor due diligence should go beyond basic document checks. It should include performance history and compliance records.
5. Review project implementation
For construction and infrastructure projects, physical verification becomes important. Ways to evaluate implementation:
- Compare actual work completion against contract specifications
- Check whether delivery timelines were met
- Monitor media reports for quality concerns or structural failures
- Conduct site visits when possible
- Review court decisions for related disputes
Sometimes fraud is not visible in paperwork — but in the quality of what was delivered.
6. Analysis
After gathering all evidence, conduct a structured analysis. Consider reviewing: audit findings from oversight bodies, payment irregularities, administrative violations, and delays without proper justification.
Evaluation should focus on:
- Contract compliance – Was the work delivered as agreed?
- Competition fairness – Was the bidding process genuinely competitive?
- Corruption risks – Any signs of bribery, conflict of interest, or collusion?
- Maladministration – Did improper conduct by officials influence the process?
Not all irregularities mean fraud. However, repeated inconsistencies across planning, bidding, vendor selection, and implementation significantly increase the likelihood of procurement misconduct.
Baca Juga: Procurement Compliance & Governance Framework Guide
11 warning signs and red flags for procurement fraud
Below are key warning signs of procurement fraud. One indicator alone may not prove misconduct, but recurring patterns deserve investigation.
- Complaints and allegations: Reports from bidders, employees, or third parties about unfair specifications, biased scoring, or insider information can signal bid rigging, favoritism, or conflicts of interest.
- Contract splitting: Large projects divided into many small contracts without clear justification may be used to avoid competition or reduce oversight.
- Overpricing: Contract values far above market rates, inflated cost components, or pricing that doesn’t match the scope of work may indicate kickbacks or hidden bribes.
- Suspicious bidding patterns: Identical formatting, similar errors, matching unit prices, exact percentage differences, bid rotation, or losing bidders becoming subcontractors can suggest collusion.
- Shell or fictitious vendors: Vendors with no clear registration, physical presence, employees, or track record may be fake entities used for fraud.
- Unjustified bid rejection: Strong bids rejected without proper reasoning, or weak bids accepted despite flaws, may indicate manipulation.
- Repeated awards to one vendor: One company consistently winning contracts without clear advantage can signal favoritism or weak competition.
- Frequent contract changes: Multiple amendments, cost increases, or scope reductions after award may point to post-contract manipulation.
- “Bait and switch” practices: Promised staff, materials, or specifications are replaced with lower-quality substitutes after contract signing.
- Irregular procurement processes: Unusual delays, rushed approvals, or deviations from standard procedures can indicate interference.
- Poor quality or abnormal billing: Substandard deliverables, duplicate invoices, inflated billing, or extremely low bids followed by cost increases are strong fraud indicators.
Read more: 7 Vendor Fraud Schemes: How to Identify and Prevent It
Common procurement fraud schemes and examples
Procurement fraud can involve internal employees, external vendors, or collusion between both. Below are common schemes explained in practical terms:
- Employee–contractor collusion / bribery: A procurement employee favors a vendor in exchange for kickbacks, gifts, or personal benefits. For example, a contract is awarded above market price after the vendor secretly pays a commission.
- Conflict of interest: A contract is awarded to a friend, family member, or related business without proper disclosure. The decision is based on personal relationships rather than objective evaluation.
- Bid rigging / manipulation: Vendors secretly coordinate bids to predetermine the winner. They may intentionally submit losing bids, rotate winners, or align pricing to eliminate real competition.
- Price fixing: Competing suppliers agree in advance to inflate prices or avoid undercutting each other, ensuring the contract value remains artificially high.
- Kickbacks and bribery: Vendors provide money, gifts, travel, or other incentives to employees in exchange for favorable scoring, inside information, or contract awards.
- Phantom vendor schemes: Fake vendors are created in the system so employees can approve fraudulent invoices and divert funds to entities they control.
- Invoice fraud / false billing: Vendors submit invoices for goods or services not delivered, inflate quantities, or duplicate billing — sometimes with insider approval.
- Product substitution: After winning the contract, a supplier delivers lower-quality goods or fewer items than specified and keeps the cost difference.
- Abnormally low bid strategy: A vendor submits an unrealistically low bid to secure the contract, then recovers profits later through change orders, cost increases, or reduced quality.
- Undisclosed subcontracting: A winning contractor outsources large portions of the work to affiliated or questionable companies without transparency.
Understanding these schemes helps organizations design stronger controls, improve vendor due diligence, and monitor procurement activities more effectively.
How to prevent and mitigate procurement fraud
Preventing procurement fraud is about building smart controls that reduce opportunity and increase transparency. Below are practical prevention measures organizations should implement.
1. Segregation of duties
Separate key responsibilities within the procurement cycle. The person approving vendors should not be the same person placing orders or approving payments.
Dividing roles reduces the risk of collusion, unauthorized spending, and unchecked decision-making.
Read more: 10 Tail Spend Management Software to Control Small Spend
2. Vendor vetting and due diligence

Thoroughly screen all suppliers before onboarding. Verify business licenses, tax registrations, physical addresses, ownership structures, and past performance records.
Proper due diligence helps prevent engagement with shell companies or high-risk vendors.
3. Utilize data analytics
Leverage technology to monitor transactional patterns. Automated systems can flag duplicate invoices, split purchases just below approval limits, abnormal pricing trends, or frequent contract amendments.
Data-driven monitoring allows early detection before losses escalate.
4. Centralized procurement system
Adopt a structured procurement system where all requests, approvals, and documentation follow standardized workflows. Centralization increases visibility, ensures policy compliance, and creates a clear audit trail.
Baca Juga: Top 7 Procurement Automation Software to Streamline Procurement Cycle
5. Internal controls and regular audits
Conduct periodic independent audits of procurement activities. Review vendor selection processes, contract modifications, and payment records. Where possible, rotate procurement staff to reduce the risk of overly close relationships with vendors.
6. Staff training and strong ethics policies
Educate employees on procurement fraud risks and red flags.
Establish a formal code of conduct, require conflict-of-interest declarations, and create safe whistleblowing channels. A strong ethical culture is one of the most effective long-term fraud prevention tools.
Read more: Procurement Maturity Model: 4 Stages to Procurement Excellence
How Mekari Expense eliminates the risk of procurement fraud
Procurement fraud often happens when controls are weak and visibility is limited. Mekari Expense’s procurement software is built to reduce these risks through structured workflows, automation, and real-time monitoring.
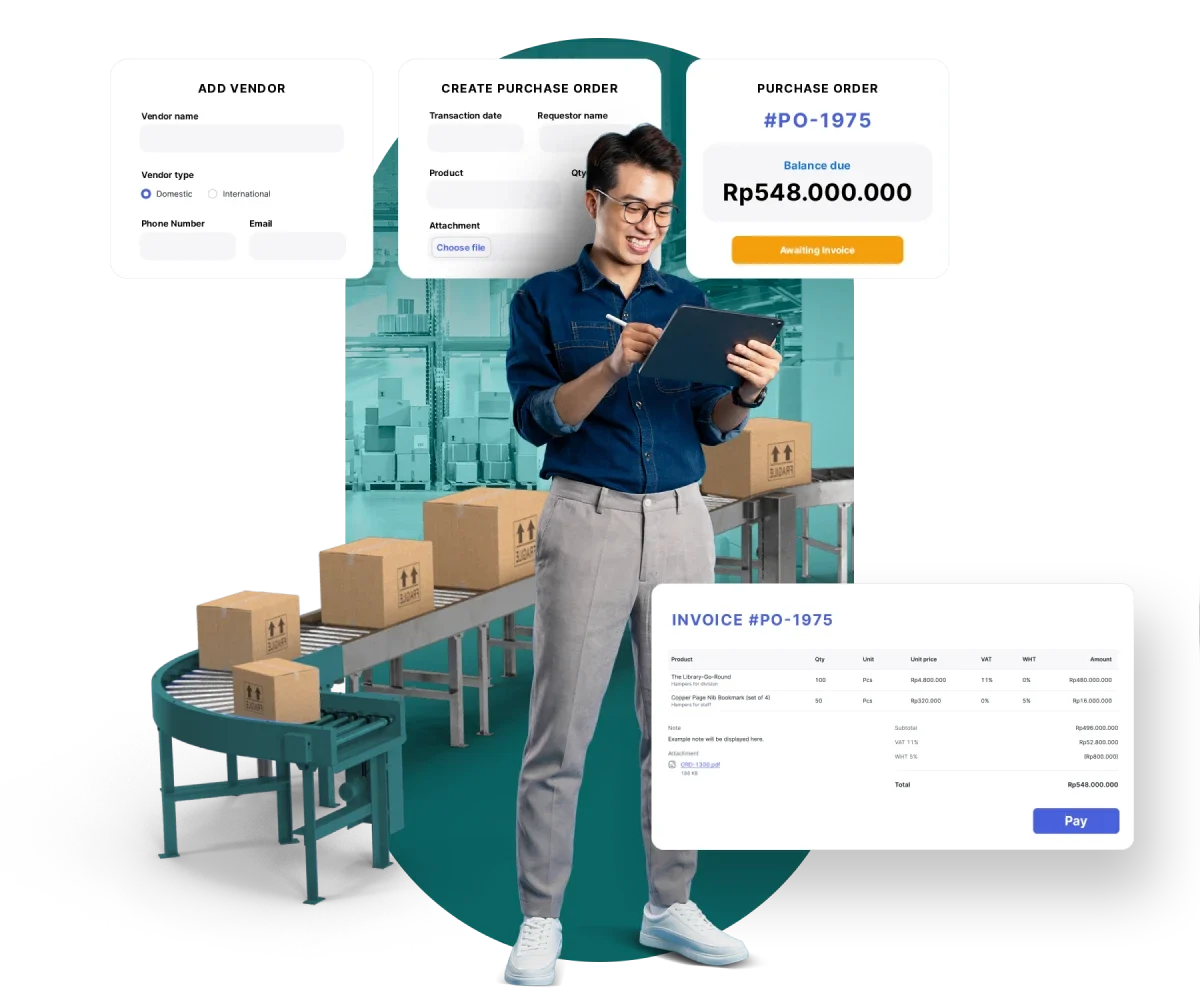
Key capabilities include:
- Verified vendor database: Only approved and registered vendors can be used, preventing fictitious supplier and phantom vendor schemes.
- Standardized product list: Fixed catalogs with predefined pricing reduce price manipulation and inconsistent entries.
- Automated multi-level approvals: Every purchase order follows structured approval flows, eliminating self-approval and unauthorized spending.
- Real-time audit trail: All transactions are automatically recorded, making it easier to detect duplicate invoices, unusual approvals, or suspicious patterns.
- Deposit & payment tracking: Real-time payment visibility helps prevent ghost payments and duplicate disbursements.
- Centralized multi-branch monitoring: A unified dashboard provides full oversight across branches and warehouses, removing operational blind spots.
- ISO 27001 data security: Certified data protection ensures procurement and financial records remain secure and tamper-proof.
With stronger controls and end-to-end transparency, Mekari Expense supports smarter procurement fraud detection through reliable, enterprise-ready procurement software.
References
Linkurious. ‘’Procurement fraud: How to spot common schemes’’
FAQ
1. What is an example of procurement fraud?
1. What is an example of procurement fraud?
An example of procurement fraud is when a procurement manager awards a contract to a vendor in exchange for kickbacks. Another common case is product substitution, where a supplier wins a bid offering high-quality materials but later delivers cheaper alternatives while charging the original price.
2. What are the indicators of procurement fraud?
2. What are the indicators of procurement fraud?
Indicators may include repeated contract awards to the same vendor, unexplained price increases, duplicate invoices, frequent contract amendments, unusually low bids followed by cost escalations, or undisclosed relationships between employees and suppliers. Patterns — not just isolated incidents — often reveal fraud risks.
3. How is procurement fraud typically detected?
3. How is procurement fraud typically detected?
It is often uncovered through internal audits, whistleblower reports, data analytics reviews, vendor due diligence checks, and irregular transaction monitoring. Technology-driven systems can also flag suspicious patterns in real time.
4. Who is most at risk of procurement fraud?
4. Who is most at risk of procurement fraud?
Organizations with high transaction volumes, manual approval processes, decentralized purchasing, or weak oversight structures face higher risk. Both private companies and public institutions can be vulnerable without strong internal controls.
5. How can companies reduce procurement fraud?
5. How can companies reduce procurement fraud?
Companies can reduce procurement fraud by strengthening internal controls, separating approval roles, verifying vendors, and using automated monitoring systems.
A structured procurement platform like Mekari Expense helps prevent fraud through verified vendors, multi-level approvals, and real-time audit trails that detect suspicious transactions early.



